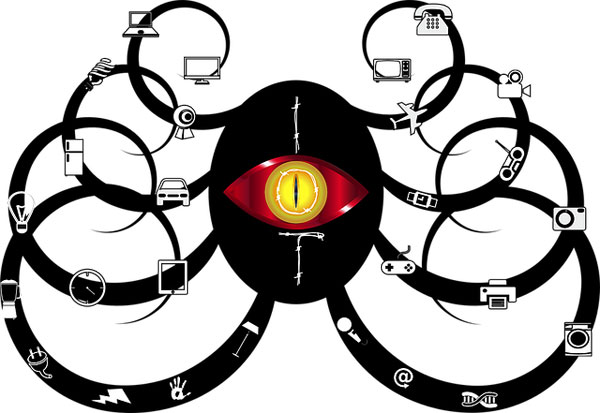
It wasn’t that long ago when people looked at Internet of Things as a fad, the idea of billions of devices connected to one another seems more like fairy-tale speech. But over the years, this technology has become more and more commonplace, both in industrial and the home. Smart TVs are becoming commonplace in the boardrooms, along with surveillance cameras, HVAC and lighting systems.
While we may look at IoT and its rise to prominence as novel, many of its common security weaknesses aren’t exactly new things. But when looking at the security concern of IoT, it differs somewhat form traditional IT security, as it requires awareness of a number of different areas, such as the following:
1. Remote Vehicle Control
As our vehicles become smarter and are linked to the internet, they also become more vulnerable to attack. Hackers have already proven that they are capable of taking control of a Jeep, changing its radio station, changing air conditioning levels, slowing the vehicle down when in motion and starting the window wipers. As a result of this news, over 1.4 million vehicles were recalled, but these same hackers said, through their research they were able to find additional vulnerabilities that they can exploit, vulnerabilities that were not addressed by the initial patch created for these recalled vehicles. Although it is said that the car industry is doing a good job in securing its vehicles, most feel it’s only a matter of time before new vulnerabilities are found and exploited.
2. Lack of Network Awareness
One major problem is that a great many organisations are completely oblivious to what exists on their network, and thus are unable to properly determine whether or not their IoT device has been misconfigured by them or a hacker. Maintaining a dashboard-like view can be rather difficult for all devices attached to a network. In most circumstances organisations are only able to see around 60% of all the devices that are connected to its network environment. This is an issue that is prevalent across a great many industries, from manufacturing to health care, to the finance sector.
3. Secure Communications
Once these IoT devices have been secured, the next security step for these devices is to ensure that all communication across the network between the cloud service, app or devices is all fully secure.
Many of these IoT devices do not use encryption when transmitting messages across a network. However, best practices state that some form of transport encryption is used, and standards like TLS be adopted. Using separate networks in order to isolate devices is another way to establish private and secure communications, so that all data transmitted is secure and confidential.
4. Remote Recording
There is this possibility that computer hackers could hack into your IoT devices and record the owner of these devices without his/her knowledge. Such information has come to light as a result of work carried out by the Central Intelligence Agency (CIA). WikiLeaks documents divulged the fact that the spy agency was aware of many zero-day exploits on IoT devices, but did not expose any information on the bugs used, as they hoped to use these vulnerabilities to secretly record conversations in hopes of acquiring information about America’s enemies or adversaries. These documents outlined vulnerabilities that existed in Android and iOS smartphones, and smart TVs. The most nerving implication is that computer hackers could also be aware of these exploits and use them for their own ends.
5. Spam
It was only several years ago when we had the first ever attack involving IoT devices that were used by a multitude of people, in order to send out in excess of 300,000 spam emails per day, across internet-connected devices, including TVs, smart refrigerators and routers. The attackers were able to send around 10 messages per device, making it extremely difficult to pinpoint and block the origin of the attack.
However, this attack was only the first of many to come,as IoT spam attacks have continued up till today.
6. Predict and Counter Security Challenges
One IoT security challenge, which can be said to be long term, is the implementation of security intelligence, not just for mitigating and detecting issues, as and when they occur, but also for predicting and protecting against potential security breaches and attacks.
Threat modelling is an adopted approach to predicting these security challenges. Other methods entail application analytics and monitoring tools, to visualise and correlate unfolding threats happening in real-time, as well as utilising AI to adjust, on the fly, to applied security strategies, based on the effectiveness of prior actions.
AUTHOR:
Uchenna Ani-Okoye is a former IT Manager who now runs his own computer support website https://www.compuchenna.co.uk.